We’ve got a screenshot of some encryption, here’s the text transcribed.
Please say what’s there.
Summary: a couple of modular equations

Jun 02
We’ve got a screenshot of some encryption, here’s the text transcribed.
Please say what’s there.
Summary: a couple of modular equations
Jun 02
Decrypt the message: 7y9rr177sluqv1r4pw
Hint:
$ at
Jun 02
We heard hellman encrypted the flag using his super secure keygen. Break it!
Summary: RSA with the lower half of the secret exponent bits leaked.
Apr 22
You get arbitrary code execution…. as long as it’s code we approve of.
Source available at blech.py
Service running on 54.234.73.81 port 1234
Summary: RSA cube root attack
Feb 06
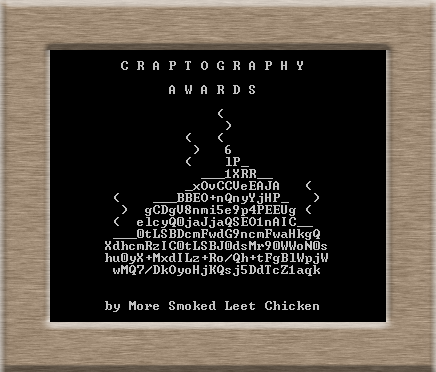
«You suck at crypto — we have an award for you!»
Today’s Nominees
Nov 19
Play with this amazing calculator: calc.challenges.polictf.it:4000
Summary: Scheme eval
Nov 19
Hensel and Gretel are looking for their new house, but the twisted seller who sold it to them decided to provide the coordinates to their new love nest only after ensuring that the couple is Smart enough to earn them.
Thus, the seller provides them with the following map and leaves Hensel and Gretel to their sorry fate.
Can you help Hensel and Gretel to reach their house providing them with the street number?
(submit the street number as a large decimal number,plain ASCII encoded so Hensel and Gretel won’t get mad trying to figure out where they should head to :) )
Summary: ECDLP on anomalous curve
Nov 19
Nov 19
Since I needed to sign a document I thought about doing it with a Chinese paintbrush… Too bad my hand is not that steady, so just in case, I re-signed it with a common pen.
Sadly I keep being forgetful, so I actually forgot where I left the two halves of the sigil I used to sign the documents, can you help me and retrieve them from the two signatures?
Please, once you got them, write them as
sha1(part1=______\npart2=_______)replace _____ with actual numbers, in decimal.
sha1 hex-encoded with lowercase letters
smallest one is part1, biggest one is part2
chinese.txt
mod.txt
steady.txt
Summary: RSA-CRT fault attack
Nov 13
The Dobbertin Challenge is issued every two years since 2006, in honor and memory of Prof. Hans Dobbertin.
A simple JSON Web Service is provided, which processes PIN codes of users. A user can send his encrypted PIN to the Web Service, which decrypts and stores the PIN. The Web Service allows to use cryptographically strong algorithms (RSA-OAEP and AES in GCM-mode) as well as algorithms with known weaknesses (RSA-PKCS#1 v1.5 and AES in CBC-mode). To create a ciphertext, a sender may choose among these algorithms.
In order to protect the confidentiality of PINs, encryption based on the JSON Web Encryption standard (link) is used. This standard allows to apply symmetric and asymmetric encryption algorithms.
You are the attacker who wants to learn the secret PIN of user Bob. You have already eavesdropped a ciphertext which contains Bob’s PIN:
eyJhbGciOiJSU0FfT0FFUCIsIml2IjoieXY2NnZ2ck8yNjNleXZpSSIsInR5cCI6IkpXVCIsImVuYyI6IkExMjhHQ00ifQ==.
ZBnPlwONWHxGDrtCxxopS4y4SrMZIAhUg3HI+SbLMxfPVRPW8yunejrkmfSLO1H/0tOx4ssggygHjG7sUfxL8A==.
i2vygn2vqFpsmep3etrD5Yh5xLP9xYhJdvn63WmHEPYChA==.
Summary: RSA-PKCS#1 v1.5 and AES-CBC padding oracles attacks
Nov 04
The famous zombie researcher “Donn Beach” almost created an immunization against the dipsomanie virus. This severe disease leads to the inability to defend against Zombies, later causes a complete loss of memory and finally turns you into one of them.
Inexplicably Donn forgot where he put the license key for his centrifuge. Provide him a new one and humanity will owe you a debt of gratitude for fighting one of the most wicked illnesses today.
https://ctf.fluxfingers.net/challenges/donn_beach.exe
ctf.fluxfingers.net tcp/2055
Summary: reverse engineering, VM, MiTM attack, AES
Oct 27
Heading up the steeple gave you and your companion a nice view over the outbreak situation in your city. But it also attracted a lot of unwanted attention. Zombies are surrounding your spot and are looking for an entrance to the building. You obviously need some bait to lure them away so you can flee safely. Solve this challenge to find out which human bodypart zombies like the most. https://ctf.fluxfingers.net/challenges/mealtime.exe
Summary: reverse engineering, TEA crypto, anti -debuging
Oct 26
3 – Zombies like PPTP
Our intel shows us that the Zombies use a MS-PPTP like protocol and luckily we could intercept a challenge-response transmission of one of the Zombie outposts. The important thing for Zombies in this war is mass! Not only brain mass but their mass. So they built their PPTP protocol compatible to all older Zombie soldiers. Luckily our science team could extract the algorithm of the challenge-response system out of a captured Zombie brain … I spare you the details, let’s just say it was not a pretty sight. And here comes your part soldier: we need the password of this intercepted transmission. With this password we were finally able to turn this war to our favor. So move your ass soldier and good luck!
https://ctf.fluxfingers.net/challenges/pptp.tar.gz
pptp.tar.gz
Summary: bruteforce LM response
Oct 25
17 – Zombieshop
A new company offers a lot of anti zombie equipment to protect yourself. Unfortunately not everyone can buy the good stuff. Only privileged users may do so. We managed to create an account, but it is not privileged. Your mission is to buy “Anti zombie Spray”.
zomboy53:killthezombies
https://ctf.fluxfingers.net:2077/
Summary: bruteforce DES