We recently intercepted a plethora of robot transmissions but they are all encrypted with some strange scheme we just can’t quite figure out. Can you crack it? Summary: small public exponent: 3
Tag: 2012
May 01
PlaidCTF 2012 – Encryption Service [300] (Password Guessing)
We found the source code for this robot encryption service, except the key was redacted from it. The service is currently running at 23.21.15.166:4433 Summary: IV predict, byte-by-byte bruteforce
May 01
PlaidCTF 2012 – Nuclear Launch Detected [150] (Password Guessing)
Our spies intercepted communications and a file between 5 of the top 10 robo-generals and their nuclear bomb server. We must recover the final launch code from the 5 robo-general’s secret codes, so we can stop the detonation! Summary: Shamir’s Secret Sharing
May 01
PlaidCTF 2012 – Format [99] (Pwnables)
Up on a hill, far away, sits the robot king of old. While he was once great, he recently has seemed to just offer simple challenges. Vanquish him and bring honor to your team! Summary: rand guessing, format string exploitation
Apr 30
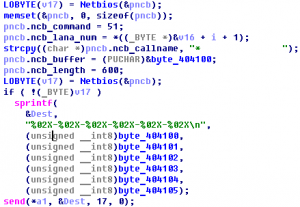
PlaidCTF 2012 – Bouncer [250] (Practical Packets)
In a recent battle we took an enemy robot hostage and examined his operating system. During the examination we found a piece of robot malware that we don’t quite understand. Can you enumerate its targets? This challenge was made by our friends at ManTech. If you enjoyed it, you might be interested in working for them. Summary: unpack …
Mar 26
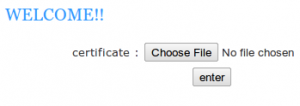
NuitDuHack 2012 Prequals – Web3.ndh
Our spy thinks that Sciteek staff is aware about the mole inside their building. He is trying to read a private file named “sciteek-private.txt” located at sciteek.nuitduhack.com:4005. Please find the .ndh attached, if you are sucessfull, reply with a message entitled “complex remote service”. Of course, your efforts will be rewarded with $2500. Maybe you …
Mar 26
NuitDuHack 2012 Prequals – executable1.ndh
Meanwhile, we got fresh news from our mystery guy. He came along with an intersting binary file. It just looks like an executable, but it is not ELF nor anything our experts would happen to know or recognize. Some of them we quite impressed by your skills and do think you may be able to …
Mar 26
NuitDuHack 2012 Prequals – sciteekadm.cap
Hopefully, we succeeded to spy some wireless communications around Sciteek building, our technical staff has attached the capture file, will you be able to exploit it? We hope that some valuable files were exchanged during the capture. Please entitle your reply “captured file”, as usual. By the way, your account has been credited with $1000. …
Mar 26
NuitDuHack 2012 Prequals – executable2.ndh
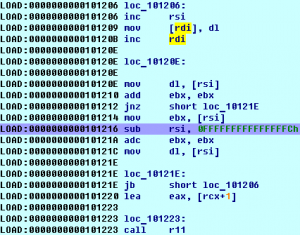
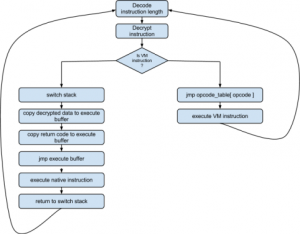
Our anonymous guy managed to get access to another bunch of files. We also need to get as much information as possible about the file itself. If you succeed, you will be rewarded with $2500 for the ndh file. executable2.ndh NDH Virtual Machine Summary: VM in the NDH VM, crackme
Feb 27
CodeGate 2012 Quals – Binary 300
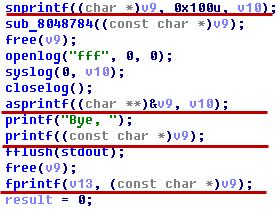
There are malicious program associated with DDoS zombie. Calcurate the sum of port numbers used for the attack. And, how many times does zombie try to attack? Answer: sum(attack_ports) * attack_count (* : multiplication) Download : 72C4DAA981E17282B12E6226A1D60162 Summary: unpack, malware analyse
Feb 26
CodeGate 2012 Quals Forensic 500 Write-up
This file is Forensic file format which is generally used. Check the information of imaged DISK, find the GUIDs of every partition. Answer: strupr((part1_GUID) XOR (part2_GUID) XOR …) Download : B704361ACF90390C17F6103DF4811E2D Forensic 500 features EWF format container with EFI GPT partition table.
Feb 26
CodeGate 2012 Quals Vuln500 Write-up
1.234.41.7:22 ID : yesMan PWD : ohyeah123 Download vulnerable binary. Vuln500 was a hardened format-string vuln with ASLR, NX-stack, no-DTORs, RO .dynamic