Brief solution ideas to the least solved Crypto CTF challenges.
Tag: rsa
Sep 19
CSAW Quals 2016 – Broken Box (Crypto 300 + 400)
I made a RSA signature box, but the hardware is too old that sometimes it returns me different answers… can you fix it for me?} e = 0x10001 nc crypto.chal.csaw.io 8002 Summary: fault attack on RSA signatures, factoring using private exponent exposure.
Sep 05
Tokyo Westerns/MMA CTF 2016 – Pinhole Attack (Crypto 500)
Decrypt the cipher text with a pinhole. $ nc cry1.chal.ctf.westerns.tokyo 23464 pinhole.7z Summary: attacking RSA using decryption oracle leaking 2 consecutive bits in the middle.
May 01
Google CTF – Spotted Wobbegong (Crypto 100)
Are you able to defeat 1024-bit RSA? public.pem Summary: breaking RSA with PCKS v1.5 padding and exponent 3.
Apr 18
PlaidCTF 2016 – Radioactive (Crypto 275)
We just got this fancy new cryptographic device and it seems to work great… for the most part. But sometimes the values it gives me are wrong. Maybe you could take a look for me. radioactive.tar.bz2 Summary: fault attack on RSA signature (not RSA-CRT)
Mar 14
0CTF 2016 Quals – Equation (Crypto 2 pts)
Here is a RSA private key with its upper part masked. Can your recover the private key and decrypt the file? equation.zip Summary: recovering RSA key from part of the private key.
Mar 13
0CTF 2016 Quals – RSA? (Crypto 2 pts)
It seems easy, right? rsa.zip Tip: openssl rsautl -encrypt -in FLAG -inkey public.pem -pubin -out flag.enc Summary: factoring 300-bit modulus into 3 primes, extracting cube roots.
May 27
CONFidence CTF 2015 – RSA2 (Crypto 500)
Find the flag data Summary: cube attack + recover python’s MersenneTwister state + leak 320/520 LSBs of one of the primes
Apr 17
PlaidCTF 2014 RSA writeup
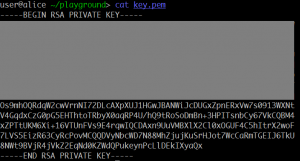
Our archaeologists recovered a dusty and corrupted old hard drive used by The Plague in his trips into the past. It contains a private key, but this has long since been lost to bitrot. Can you recover the full key from the little information we have recovered?
Jun 02
PHD CTF 2013 ReStART (400)
We heard hellman encrypted the flag using his super secure keygen. Break it! Summary: RSA with the lower half of the secret exponent bits leaked.
Apr 22
PlaidCTF 2013 Blech (Crypto 200)
You get arbitrary code execution…. as long as it’s code we approve of. Source available at blech.py Service running on 54.234.73.81 port 1234 blech.py Summary: RSA cube root attack
Nov 19
PoliCTF 2012 Crypto 100
Since I needed to sign a document I thought about doing it with a Chinese paintbrush… Too bad my hand is not that steady, so just in case, I re-signed it with a common pen. Sadly I keep being forgetful, so I actually forgot where I left the two halves of the sigil I used …
Nov 13
Dobbertin Challenge 2012
The Dobbertin Challenge is issued every two years since 2006, in honor and memory of Prof. Hans Dobbertin. http://cryptochallenge.nds.rub.de:50080/ A simple JSON Web Service is provided, which processes PIN codes of users. A user can send his encrypted PIN to the Web Service, which decrypts and stores the PIN. The Web Service allows to use …
- 1
- 2