The Plague is running a betting service to build up funds for his massive empire. Can you figure out a way to beat the house? The service is running at 54.197.195.247:4321.
Tag: bruteforce
Jun 17
Defcon CTF Quals 2013 – All Web Challenges (3dub)
Summary: 3dub (1) – babysfirst: SQLite SQL injection 3dub (2) – badmedicine: Stream cipher bit flipping 3dub (3) – hypeman: Rack/Sinatra session secret disclosure 3dub (4) – rememberme: Bruteforce 3dub (5) – worsemedicine: Block cipher bit flipping
Nov 04
Hack.lu 2012 CTF Challenge #12 (500)
The famous zombie researcher “Donn Beach” almost created an immunization against the dipsomanie virus. This severe disease leads to the inability to defend against Zombies, later causes a complete loss of memory and finally turns you into one of them. Inexplicably Donn forgot where he put the license key for his centrifuge. Provide him a …
Oct 26
Hack.lu 2012 CTF Challenge #3 (450)
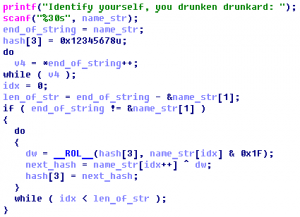
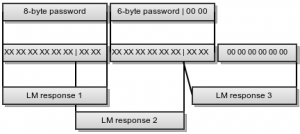
3 – Zombies like PPTP Our intel shows us that the Zombies use a MS-PPTP like protocol and luckily we could intercept a challenge-response transmission of one of the Zombie outposts. The important thing for Zombies in this war is mass! Not only brain mass but their mass. So they built their PPTP protocol compatible …
Oct 25
Hack.lu 2012 CTF Challenge #17 (400)
17 – Zombieshop A new company offers a lot of anti zombie equipment to protect yourself. Unfortunately not everyone can buy the good stuff. Only privileged users may do so. We managed to create an account, but it is not privileged. Your mission is to buy “Anti zombie Spray”. zomboy53:killthezombies https://ctf.fluxfingers.net:2077/ Summary: bruteforce DES
Feb 26
CodeGate 2012 Quals Net400 Write-up
Because of vulnerability of site in Company A, database which contains user’s information was leaked. The file is dumped packet at the moment of attacking. Find the administrator’s account information which was leaked from the site. For reference, some parts of the packet was blind to XXXX. Answer : strupr(md5(database_name|table_name|decode(password_of_admin))) (‘|’is just a character) Download …
Feb 13
IFSF CTF #7 (X99) Write-up
this is one of their machines which have very sensitive informations , try to get for us the password 208.64.122.27 PORT : 3000 X99 carries a synthetic vulnerability that allows a char-by-char password bruteforce.
Feb 13
IFSF CTF Small Challenges (#4, #5, #6, #14, #15)
Contents #4 ER #5 Change #6 Call me #14 Seek me #15 Embedded docs
Apr 09
Nuit du hack 2011 CTF Forensic
Forensic 100 On a dumpe la RAM d’une machine sur laquelle tournait un serveur VNC. Le but est de recupere le mot de passe de ce serveur. * * * We have dumped the RAM of a Machine on which was running a VNC server. The goal is to get the password of that VNC …
Mar 07
Codegate CTF 2011 Crypto300 Writeup
Description: we are investigating an illegal online gambling site. To find any evidence to support for illegal gambling, we must access the oracle database with administrator privileges. The suspect says that he does not know the administrator password, but we know for sure that he is lying. The password is estimated to be longer than …
Oct 30
Hack.lu 2010 CTF Challenge #8 Writeup
Sad Little Pirate (150) Our sad little pirate haes lost his password. It is known that the pirate has just one hand left; his left hand. So the paessword input is quite limited. Also he can still remember that the plaintext started with “674e2” and his password with “wcwteseawx” Please help the sad pirate finding …
Oct 30
Hack.lu 2010 CTF Challenge #18 Writeup
Digital Treasure Chest (300) You were asked to pentest the 1.1 beta-version of the digital treasure chest. Finding an authentication bypass appears to be trivial to you. pirates.fluxfingers.net 6969/tcp $ nc pirates.fluxfingers.net 6969 010 WELCOME. Please Enter your secret digits 0 555 Wrong credentials If we try some more numbers, we will get: $ nc …