Continuing on from Eucalypt Forest – can you break Message Authentication in Wolf Spider wolf.py Summary: forging signatures by exploiting CBC padding oracle and hash length extenstion
Tag: sha1
Feb 09
Olympic CTF 2014 GuessGame (300)
Be careful, it’s cheating! nc 109.233.61.11 3126 Summary: discrete logarithm with group oracle
Oct 26
Hack.lu 2012 CTF Challenge #3 (450)
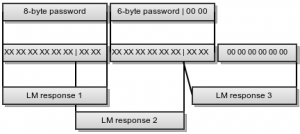
3 – Zombies like PPTP Our intel shows us that the Zombies use a MS-PPTP like protocol and luckily we could intercept a challenge-response transmission of one of the Zombie outposts. The important thing for Zombies in this war is mass! Not only brain mass but their mass. So they built their PPTP protocol compatible …