Login as admin and get the flag1. mmaddress.7z Summary: breaking HMAC-CRC512
Tag: web
Feb 02
Olympic CTF Sochi 2014 Registration is Open
Let there be Olympics MSLC proudly presents…Alright, do we even need words here? Game starts: February 7th, 2014 16:14 UTC (yeah yeah, those Sochi number freaks… it’s 20:14 in MSK timezone) Game ends: February 9th, 2014 16:14 UTC Sign up: https://olympic-ctf.ru/ Prize set: 1500 USD, 1000 USD, 500 USD. Expect decent tasks. Twenty of them.
Jan 07
Sudden CTF syndrome
Happy new 2014 and merry Orthodox Christmas if you’re religious ;-D Maybe you already know hack you and hack you too, so I won’t even say that hack you is an individual CTF that we originally held for our university freshmen and opened it for everyone interested in the world. Couple days after this New …
Jun 17
Defcon CTF Quals 2013 – All Web Challenges (3dub)
Summary: 3dub (1) – babysfirst: SQLite SQL injection 3dub (2) – badmedicine: Stream cipher bit flipping 3dub (3) – hypeman: Rack/Sinatra session secret disclosure 3dub (4) – rememberme: Bruteforce 3dub (5) – worsemedicine: Block cipher bit flipping
Oct 04
Announcing hackyou CTF
It’s fall already and that means the new CTF season is starting, and so is the new academic year in our university. This is the time when we want to attract more freshmen into our CTF tarpit ;-D So we are running – a CTF. But it’s not just for them. Wouldn’t it be fun …
Feb 26
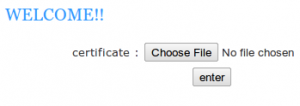
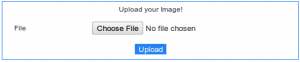
CodeGate 2012 Quals – Vuln 200
This web challenge is again about uploading. Our aim was to get shell. Summary: upload php shell, read the key.
Feb 26
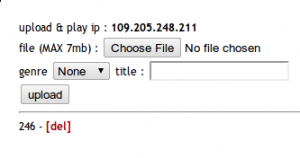
CodeGate 2012 Quals – Vuln 100
This challenge is a web service where one can upload mp3 files and listen to them. Our aim is to get admin’s song. Summary: sql injection
Oct 31
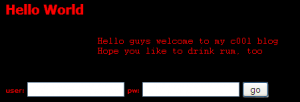
Hack.lu 2010 CTF #13 (My Cool Blog) writeup
Captain Rumbarrel is shocked because he found out that the filthy pirate Boozybold has stolen a whole shipment of rum! So Rumbarrel wants his revenge by hacking Boozybolds cool blog. Unfortunately he can not hack, so help him and get 250 gold coins! From main page of his cool blog, we get three main points: …
Oct 31
Hack.lu 2010 CTF #17 (Brainfuck) writeup
You found a backdoor on Captain Brainfuck’s webspace. Exploit it and read his secret file! The page only says ‘happy hacking’, so what would we be doing without its source… [source mirror] “Source” in fact is a zip archive with php code appended: PK <..zip binary trash..> <?php @ob_clean();$z=zip_open(__FILE__); eval($f=zip_entry_read(zip_read($z),1000));@ob_end_flush();?> It simply reads itself (the …
Sep 21
Leet More 2010 Oh Those Admins! writeup
Category: web-vuln?! http://vos.uz/oh_those_admins/ http://vos.uz/oh_those_admins/index.php.txt The php script takes a ‘password’ as input, calculates its raw (binary) md5, performs SQL query: SELECT login FROM admins WHERE password = ‘$raw_md5′ and if it returns something, gives us full list of admins. Raw md5 can contain any chars, and script puts them in query as is – it’s …