Forensic 100 On a dumpe la RAM d’une machine sur laquelle tournait un serveur VNC. Le but est de recupere le mot de passe de ce serveur. * * * We have dumped the RAM of a Machine on which was running a VNC server. The goal is to get the password of that VNC …
Tag: 2011
Apr 04
Nuit du hack 2011 CTF Crypto 300
Crypto300 (150 pts.) source Python source code is very clear and concise, and could sometimes bring out lots of clues. This is particularly true for this challenge. Summary: key exchange algorithm based on permutations (braid based cryptography), has some vulnerabilities
Mar 09
Codegate CTF 2011 Vuln 300
This challenge was an exploitation of suid binary. binary Summary: ROPing buffer overflow with NX and ASLR
Mar 08
Codegate CTF 2011 Binary 200
Let’s open this PE-file in IDA Pro. There is TLS-callback at address 0x00401450. TLS-callback is just anti-debugging trick (with SEH, dynamic import etc), so we can skip it and start execution from entry point: 0x00401000. On the entry point we can see some decoding cycle and one call at address 0x00401058. If we go into …
Mar 08
Codegate CTF 2011 Issue 500 (bootsector)
Find a key. [link to submit form] binary $ file challenge.bin challenge.bin: x86 boot sector, code offset 0xc0 Summary: bootsector with password check, bruteforcing 2 bytes hash.
Mar 08
Codegate CTF 2011 Crypto 400
The attacker got a secret! File Summary: Padding oracle attack analysis
Mar 07
Codegate CTF 2011 Forensic 300, Issue 300
Forensic 300 Description: We are investigating the military secret’s leaking.we found traffic with leaking secrets while monitoring the network.Security team was sent to investigate, immediately. But, there was no one present. It was found by forensics team that all the leaked secrets were completely deleted by wiping tool.And the team has found a leaked trace …
Mar 07
Codegate CTF 2011 Mini writeups
Some mini writeups on Codegate 2011 Prequals: Issue100,200, Net100,200, Crypto100,200.
Mar 07
Codegate CTF 2011 Crypto300 Writeup
Description: we are investigating an illegal online gambling site. To find any evidence to support for illegal gambling, we must access the oracle database with administrator privileges. The suspect says that he does not know the administrator password, but we know for sure that he is lying. The password is estimated to be longer than …
Jan 20
Padocon CTF 2011 Binary500 Writeup (300)
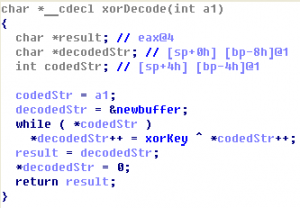
The challenge consists of a windows binary and connection details: HOST : 168.188.130.216 PORT : 888 Binary (Daemon.exe) Summary: reversing the algorithm with some encryption and coding a client
Jan 19
Padocon CTF 2011 Binary100 Writeup (200)
This task we were given a binary and a host/port where it is running: HOST : 168.188.130.217 PORT : 8080 Binary Note: At the beginning of the contest, there was no binary. But nobody solved it and the binary was added, I guess it’s because of strange format of the input. Summary: reversing (or guessing) …